Cybersecurity Threats to Watch Out For
Cybersecurity is a very important topic, especially now that so many businesses are relying on their computer systems to do most of their work. Regardless of whether you are a small company or a large corporation, there are many cybersecurity threats you should watch out for.
From phishing scams and malicious software to ransomware attacks, this article will outline what you should be looking for in order to keep your information safe.
Phishing Scams Cybersecurity Threats
Cybersecurity threats to watch out for include phishing scams, smishing, and whaling. Each has their own specific techniques, but they share common characteristics.
In a phishing scam, an attacker tricks the recipient into providing private information. Typically, the attacker impersonates a company or an individual. The fake email or web page may contain links to a legitimate site or it may be completely fake.
Spear phishing, also known as spoofing, is a form of phishing where the victim is contacted by an email address that looks like a real organization. This message will ask the user for personal details, such as their password or financial data.

Spear phishing is often a deceptive method, and successful messages use a combination of misspelled URLs, poorly written copy, and threats. These are intended to evoke fear or encourage the user to take action.
Whaling attacks, on the other hand, do not rely on fake URLs. Instead, the attacker uses sensitive data to craft the message. Such information can be found in public sources, such as social networking sites and corporate databases.
Phishing scams can involve several methods, such as sending fraudulent emails to users on social networks. The attack may include malicious attachments or a link to a fraudulent site.
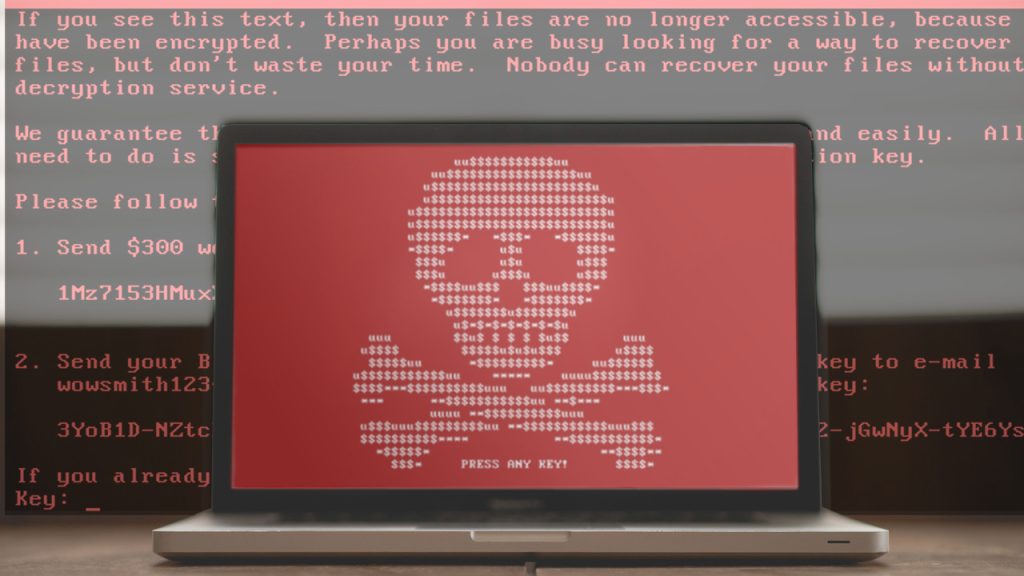
Malware and Ransomware Attacks
Ransomware is a form of cybercrime that locks up data. The attacker demands a ransom, usually in the form of a cryptocurrency, to unlock the files. Once they’re locked, they cannot be unlocked without the attacker’s key.
These cybersecurity threats are becoming more common, and they can be costly. Victims may incur legal fees, network modifications, or lost productivity. In addition, news of a cyberattack can turn customers against a company.
It’s important to take preventive measures and keep all software up-to-date. Additionally, you should avoid clicking on links in spam, text messages, and third-party app stores.
Cybercriminals are becoming more sophisticated and savvy. They know that if they can get inside a business, they can find its most valuable information.
They can also prey on human psychology. Social engineering attacks are often a part of the criminal’s campaign. For example, the Reveton virus used its webcam to mimic a user’s behavior. When the victim attempted to film themselves, the system reportedly accused them of illegal activity.
Public infrastructure, such as utilities, are a big target. This includes the National Health Service, which was affected by the WannaCry malware attack.
Utilities have access to large amounts of money. If they lose access to that money, they can suffer financially.
Unsecured Wi-Fi Networks
There are a number of threats to users of unsecured Wi-Fi networks. These threats are designed to gather data, change passwords, and destroy valuable information. Luckily, you can protect yourself by following a few simple steps.
The first step is to avoid using unsecured Wi-Fi. In fact, many experts recommend never connecting to an unsecured network.
Second, you should use a VPN to encrypt your data while moving between networks. This will lower your risk of password leaks. Lastly, you should also keep your operating system updated. Many OS updates include important security patches.

Despite this, there are still a few ways you can get hacked. A common tactic is to send malicious emails. Another method involves hijacking your browser.
Unsecured Wi-Fi can also be used for more serious crimes. Hackers can access your accounts, causing financial liability. They can also spy on your web activity.
Finally, an unsecured Wi-Fi network can be used for distributing malware. Malware can be planted on your computer, stealing personal and financial data.
Finally, you should also protect yourself with a good antivirus program. Most devices are equipped with default administrator passwords, so it’s easy to pick up malware without even knowing it.
For the same reason, if you’re going to use a public Wi-Fi network, make sure you know which ones are secure and which are not.
You can be protected from this and dozens of other similar cyber attacks with antivirus programs. By clicking here, you can access the most used antivirus programs. Want to read more helpers contents.